It's often said that a fool and his money are soon parted but there are occasions when stress, bad news or just plain fatigue can adversely affect our ability to make sound judgement calls. Sadly, there are those who take advantage of – or even actively create – such situations to make a quick buck. In today's always-connected online world, it might be tempting to believe that hustlers have all-but abandoned telephone fraud in favor of email versions of the age-old Nigerian 419 scam, malware-infested instant messages and websites, or infected digital downloads ... but telephone sucker games are very much alive and well. Researchers from Nagoya University and Fujitsu have spent the last few years developing an automated detection system that alerts the recipient to possible phone phishing scams. After successful simulation testing, the team has now announced plans for household field trials.
Confidence tricksters persuading folks to volunteer personal information or financial details over the phone, or to buy something they don't really want or need, is said to be almost as old as the telephone system itself. Fraudsters might pretend to be a phone company support representative who makes it appear that your handset is faulty, or claim to be a Microsoft technician looking to gain remote access to a PC, or just leave a message about a failed parcel delivery attempt which asks you to call back and make alternative arrangements (via a premium rate number).
Being informed and aware can help guard against being duped by such scams (by paying a visit to online scam-busting resource Snopes.com, for instance). But even the most vigilant can fall foul of the often plausible patter from an official-sounding caller, particularly in situations where the perpetrator might cause a high degree of stress by delivering unexpected bad news.
Nagoya University and Fujitsu first announced a research partnership in November 2009 aimed at developing automated technology to identify situations where one party might overtrust the other. In March of this year, the team announced the successful development of the world's first system capable of analyzing phone conversations and automatically highlighting suspect situations. The system looks for changes in a caller's voice pitch and level, together with keywords often used and repeated in phone scams.
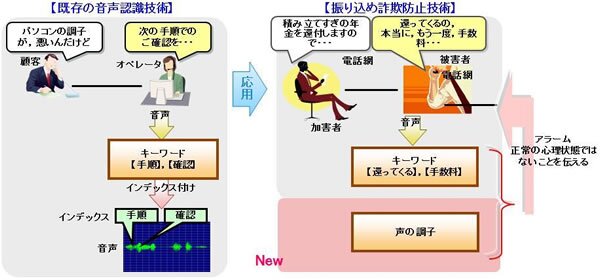
Subsequent verification simulation testing undertaken in collaboration with the National Police Agency of Japan and the Bank of Nagoya found the technology to be over 90 percent accurate in detecting situations of overtrust.
Now the research team is about to enter field trials of the system. With the cooperation of the Okayama Prefectural Police, the Okayama Prefecture Information Communications unit of the National Police Agency's Chugoku Regional Police Bureau, and The Chugoku Bank, over 100 monitored households will shortly be equipped with special devices connected to landlines. If a potential remittance-soliciting phone phishing scam is detected, a synthesized voice will warn the recipient to exercise caution.
At the same time, an email will also be sent to alert selected family members, followed by notifications to the police, banks and other relevant institutions. Each party can then take steps to protect the compromised individual from personal or financial harm. The police, for example, could arrange to visit the recipient of the call, and the banks or credit companies could look out for any suspicious transaction activity or temporarily freeze assets.
Any necessary improvements or tweaks to increase system accuracy will be applied throughout the field trials, and upon successful completion, the team will begin looking at the commercialization of the technology.
The next step in the research program (which will continue until March 2015) is to explore ways to actually prevent telephone fraud before it occurs.
Source: Fujitsu






