In the near future, an F-35 fighter plane on a routine flight kicks in its afterburners and it goes supersonic. Suddenly, there's an almighty bang as one of the turbine blades in the jet engine disintegrates and within seconds the US$85 million plane is tearing itself to pieces. Is it an accident or sabotage? According to researchers at Ben-Gurion University (BGU), this scenario could be an example of a new type of cyber warfare where saboteurs can fool 3D printers into creating self-destructing parts that are indistinguishable from the real thing.
We tend to think of cyber attacks as something that involves stealing personal details or pilfering bank accounts, but with the world depending more and more on automated factories, robots, and the internet of things, the capacity of villains to do direct physical harm continues to grow. One example of this is spoofing 3D printing facilities into producing components that are designed to fail at critical moments.
Part of an international team that includes, BGU, the University of South Alabama, and Singapore University, the cyber security experts were considering the vulnerability of 3D printers to malicious hackers. At first they seemed not very susceptible to attack, but that soon changed.
"Initially we focused on checking whether the 3D printer can be hacked," says Professor Yuval Elovici, director of the Deutsche Telekom Innovation Lab and the BGU Cyber Security Research Center. "Quickly, we realized that such an attack cannot scale due to the huge variety of 3D printers, so we decided to focus on how attackers may intervene in a generic way in the process between design and production."
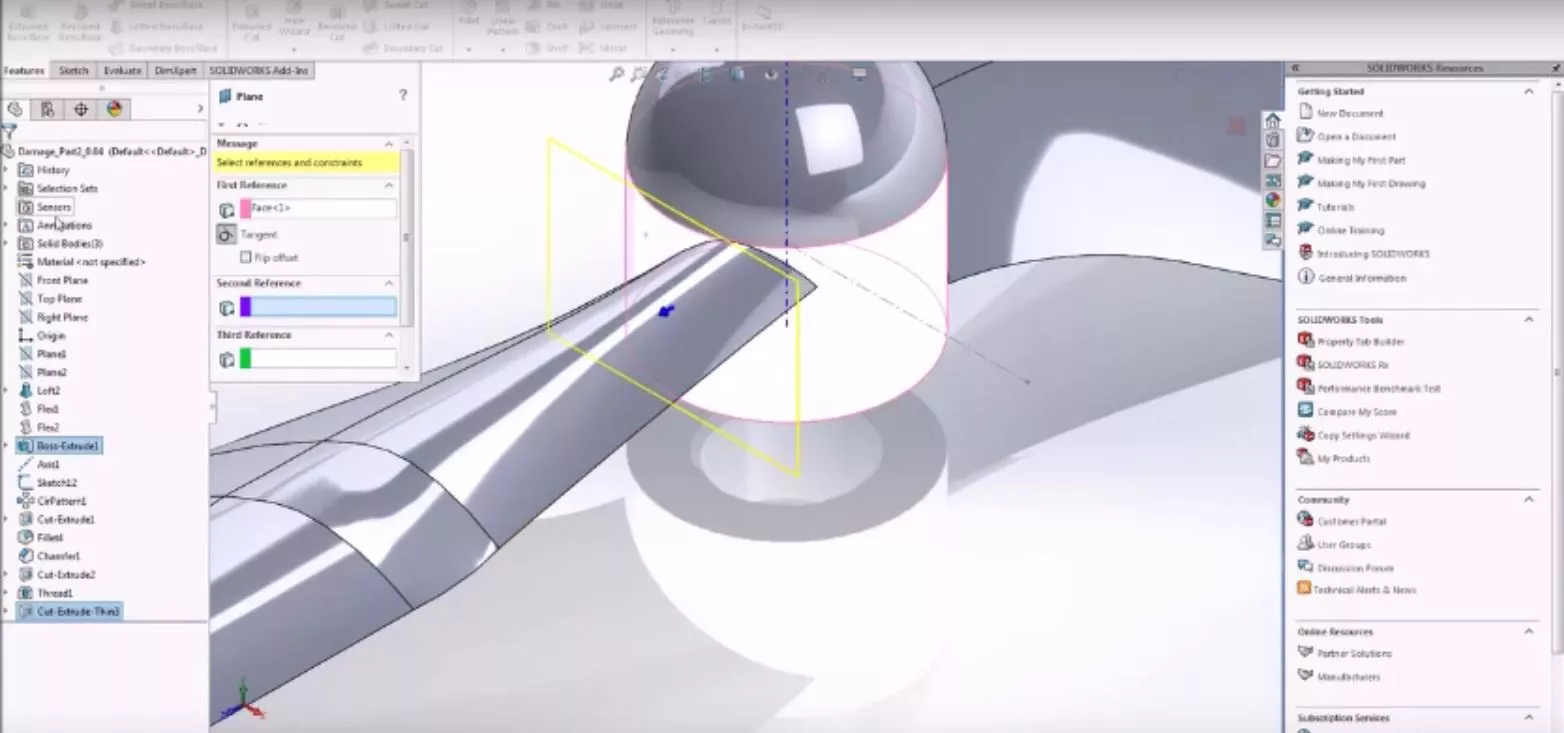
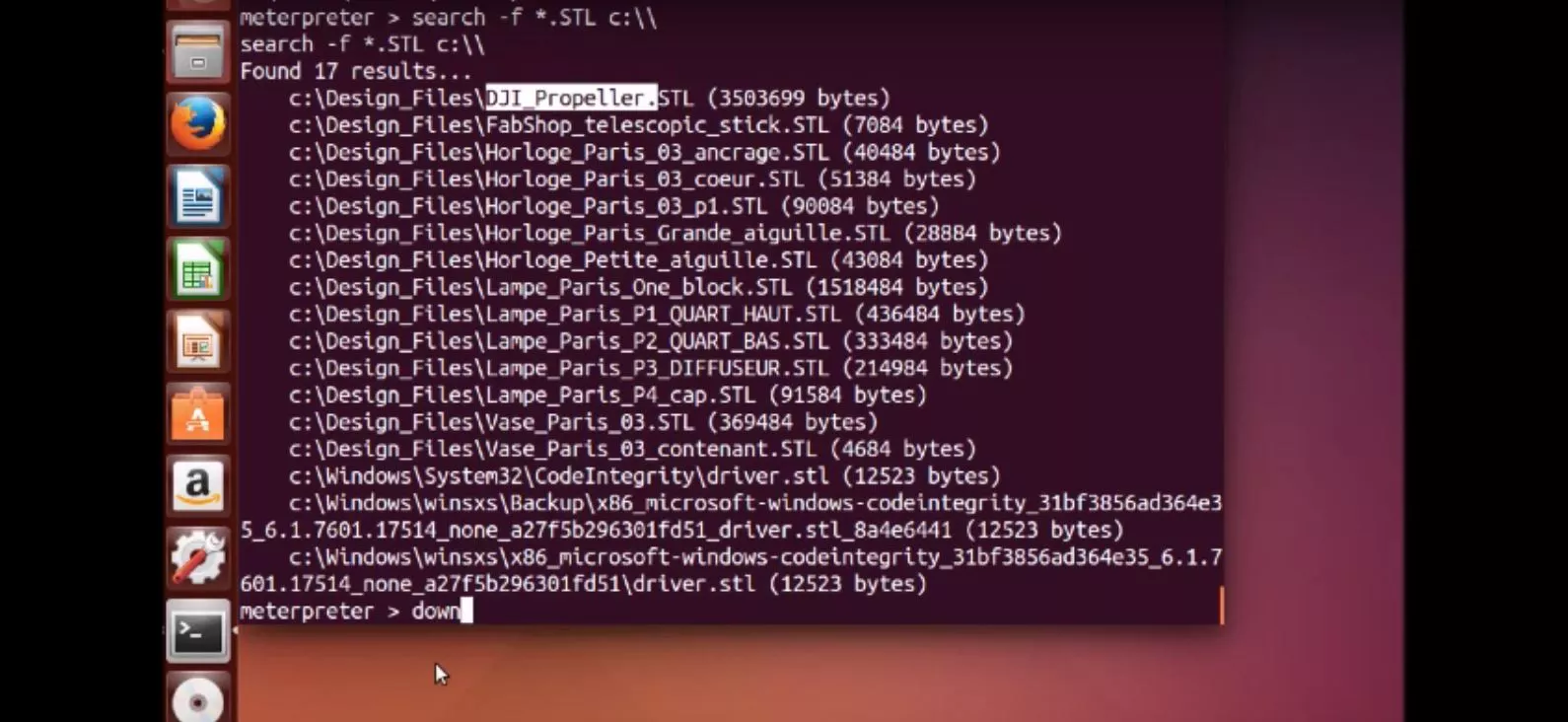
Instead of attacking the machines directly, the researchers went for the more vulnerable parts of the design and production cycle. They used a phishing attack to plant a malicious .exe file in the email of the simulated victim. When opened, they were able to gain access to the victim's personal computer, search for the design files for a drone propeller and download them.
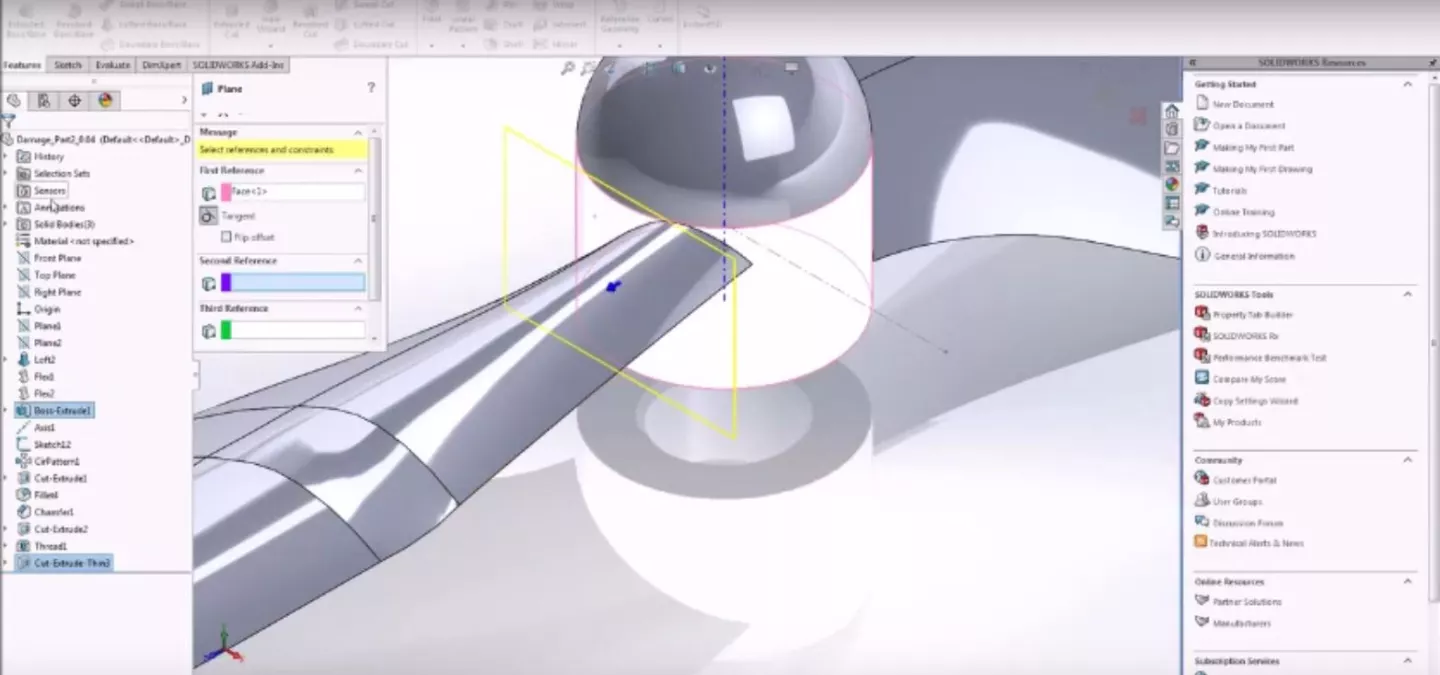
Using the files, the researchers redesigned the propeller. It still looked like the original to the casual eye, but they had introduced 0.1 mm cavities into the blades and the joints so that when maximum stress was applied in flight, they'd quickly weaken and break.

According to the team, when the propeller was printed and installed on a commercial drone it looked indistinguishable from the untampered propellers, but it failed as planned after two minutes.
"Imagine that an adversary can sabotage functional parts employed in an airplane's jet engines," says Elovici. "Such an attack could cost lives, cause economic loss, disrupt industry, and threaten a country's national security. Before printing an object, there is a need to check that the file was not modified, and there are many cryptographic means that can be used in order to achieve this goal."
The team's paper can be found here.
The video below shows how the 3D hacking scenario was carried out.
Source: BGU