Researchers at the University of Cambridge and Toshiba's European research branch have found a way to speed up the rate at which data can be securely transmitted using quantum cryptography. It's a development that could pave the way to faster, ultra-secure communications that are impossible to spy on.
Many of the encryption methods that keep our online data safe rely on a digital key which is very hard for computers to crack – for instance, requiring the identification of two very large prime numbers, which standard computers are very poor at. But if a powerful quantum computer were to be built, it could crack these types of code with ease and jeopardize the safety of our digital communications.
The only encryption method that has been proven to be completely secure if applied correctly – quantum computers or not – is the so-called "one-time pad." Here's how it works: first, a secret digital key is created consisting of a completely random sequence of bits. The key is then securely sent to the receiver, and kept private. Now, the sender can encrypt his message by adding the message's bits to the random bits of the key. Under these conditions, the code is deemed truly uncrackable.
Keeping the key secret can be a challenge, but quantum physics can come to the rescue. That's because the weird and wonderful properties of quantum mechanics make it so that if someone were to try and intercept it, the key itself would change and both the sender and the receiver would immediately notice.
Up to now this one-time key, which ideally must be at least as long as the message itself, could only be sent at very slow data rates of a few hundred bits per second. Luckily, researchers Lucian Comandar and colleagues have now found a way to increase that bitrate ten thousand-fold up to a much more workable 1Mbps, in an important step toward practical and secure digital communications.
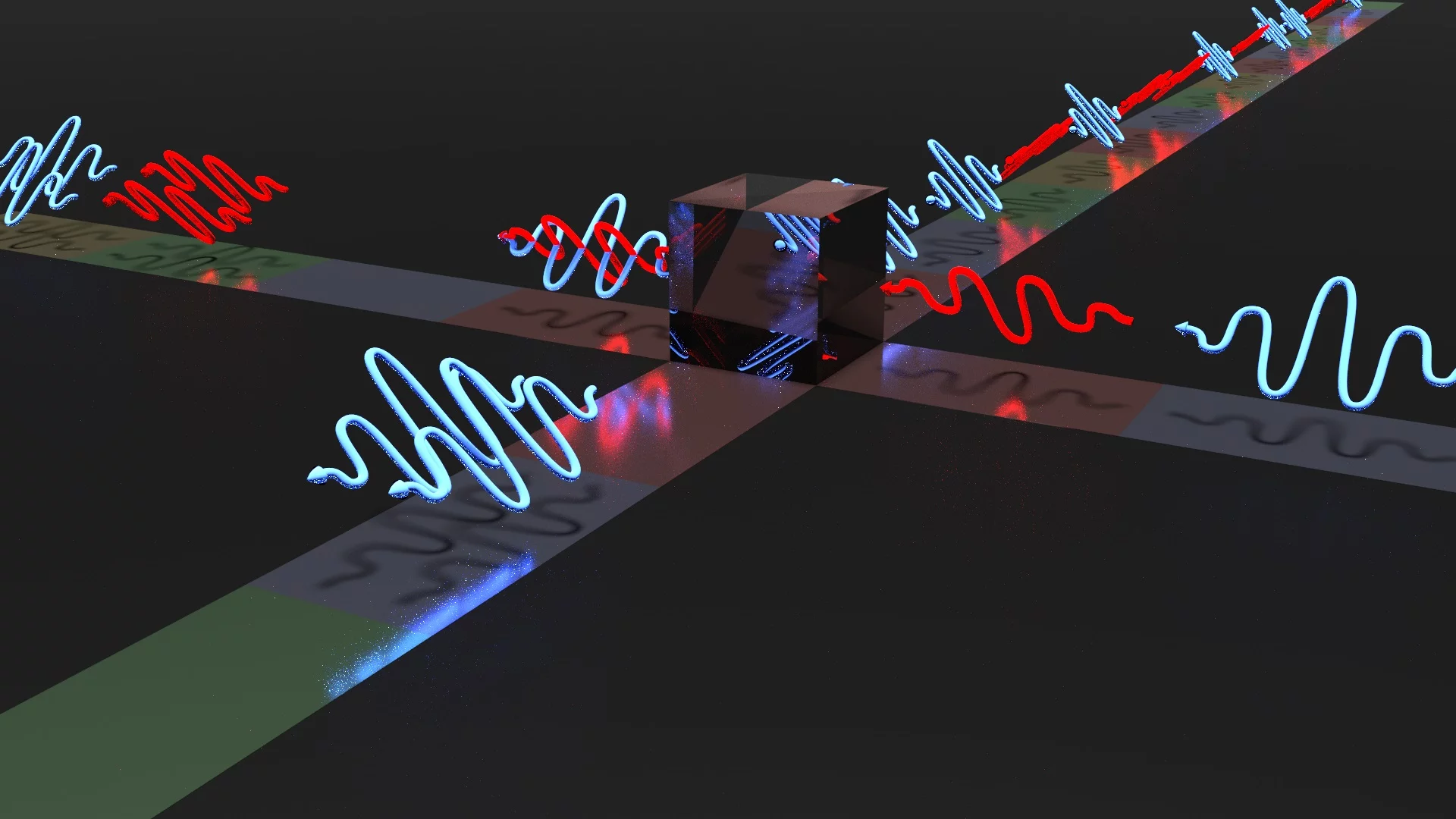
The data transmission rates for the secret key have been slow because the secure protocol (named "measurement-device-independent quantum key distribution," or MDI-QKD) adds complexity to the system in the form of a second photon detector and an entity between sender and receiver that must measure photons coming from both parties.
"The protocol relies on interfering photons on a beamsplitter," Comandar tells Gizmag. "Practically, the protocol works only with coincidence counts between two detectors rather than single counts on one detector. And because the probability of a single count is lower than [100 percent], the probability of a coincidence count is even lower."
Moreover, laser pulses can be jittery and unpredictable: in this case, a 35 picoseconds pulse could shift by as much as 10 picoseconds in time, introducing noise that ground the transfer rates almost to a halt.
The researchers were able to increase transfer speeds considerably by overlapping two laser pulses: by injecting photons from another laser into the first one, the researchers were able to trigger the pulses at a precise time. These shorter, more precise pulses enable much faster data rates.
"The protocol I have been working on is still in its development stages," Comandar tells us, "it was actually proposed only four years ago and the first experimental implementation was three years ago. So there is still room for improvement."
The next steps will include trying to implement improvements in all of the system's components.
A study describing the advance appears in this week's edition of the journal Nature Photonics.
Source: University of Cambridge