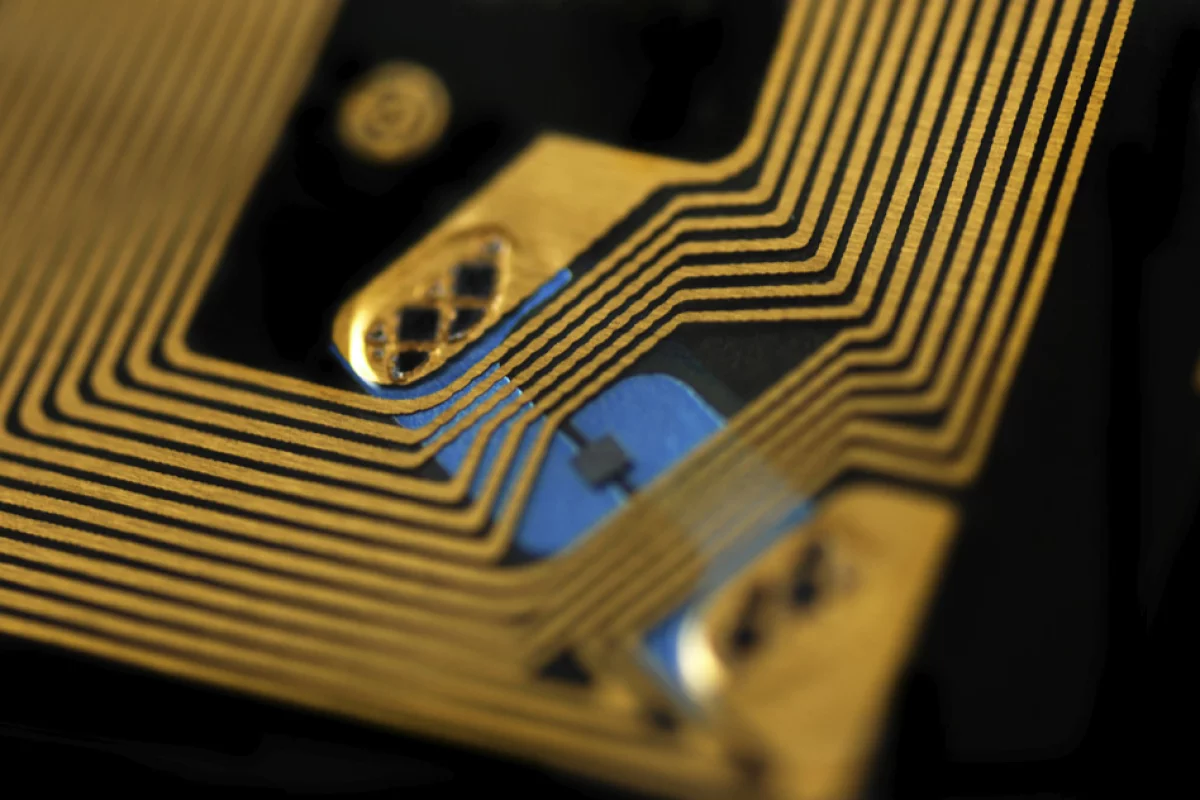
Radio frequency identification (RFID) chips have made cashless payments commonplace and opened the way to automatic inventory control. However, they've also made it possible for credit card details and other private information to be stolen wirelessly. To make things a bit more secure, MIT and Texas Instruments are developing an "unhackable" RFID chip that's designed to fend off information-stealing attacks.
Even if information on a chip is covered by supposedly unbreakable encryption, the keys for using that encryption are still very vulnerable – especially in a wireless environment. RFID tags are vulnerable to a number of hacking strategies called side-channel attacks. These involve studying patterns of memory access or fluctuations in power usage as the chip carries out encryption operations and using the information to deduce the password keys.
"The idea in a side-channel attack is that a given execution of the cryptographic algorithm only leaks a slight amount of information," says Chiraag Juvekar, a graduate student in electrical engineering at MIT. "So you need to execute the cryptographic algorithm with the same secret many, many times to get enough leakage to extract a complete secret."
Such automated attacks can have very expensive consequences, but there are already countermeasures against them. Unfortunately, they produce their own vulnerabilities. For example, some RFID chips reject password attempts after a number of failures and others regularly generate a new pair of password keys using random number generators to make them more difficult to guess.
However, the MIT team points out that these leave chips open to "blackout" or "power glitch" attacks. Since RFID chips are powered by the radio beam of the scanning device, the attacker can switch the chip off and on thousands of times before it's able to change its passwords. This also wipes the chip's memory and lets the intruder run the same side-channel attack using the same key without getting locked out or dealing with a new key because the chip can't remember what it was working on.
Texas Instruments has already constructed a number of prototypes of the new chip based on specifications from the MIT team. It overcomes side-channel attacks and power-glitch attacks in particular by providing the chip with an onboard power supply and a non-volatile memory, so it can't get electronic amnesia when switched off.
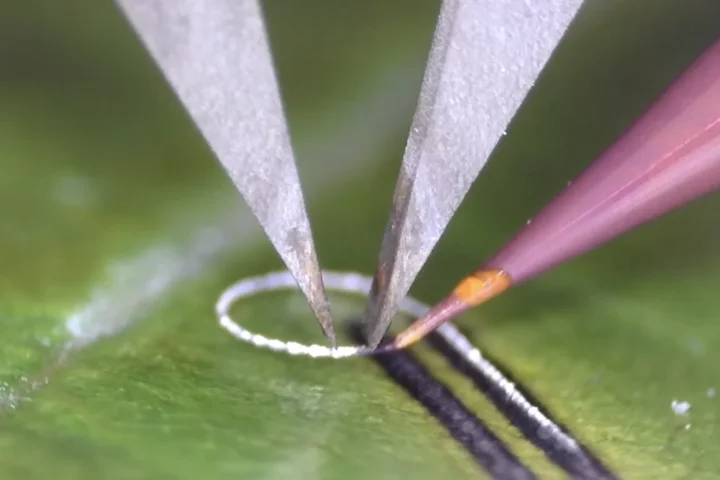
The team managed this by using ferroelectric crystals, which consists of molecules set in a three-dimensional lattice. The cells in the crystal lattice carry positive and negative electric charges. These are normally aligned in a random pattern, but when an electric field is applied, the cells can be lined up to represent the ones and zeros of binary code. Since the crystals retain their polarization when the field is turned off, they can act as a memory.
MIT says that another property of the crystals is that they can act as a capacitor, which means they can retain an electric charge like a battery that the chip can run on when the scanning beam is off. In this case, the chip has a bank of 3.3 V ferroelectric cells and 571 1.5-V cells. The 3.3 V cells power the chip long enough to carry out whatever computations it was working on when the beam switched off, while the 1.5 V cells act as a non-volatile memory.
The clever bit is that when the chip is switched off and on, the first thing it does is recharge itself, so it can't be drained of power by repeated attacks. It can then complete its last task and if it happens to be installing a new encryption key, that gets priority, so a power-glitch attack won't be effective.
The team says that this added security comes at a cost. The added task of recharging the capacitors and completing computations slows the chip down, but they say that it can still manage 30 readouts per second, which is practical.
"In the age of ubiquitous connectivity, security is one of the paramount challenges we face," says Ahmad Bahai, chief technology officer at Texas Instruments. "Because of this, Texas Instruments sponsored the authentication tag research at MIT that is being presented at ISSCC. We believe this research is an important step toward the goal of a robust, low-cost, low-power authentication protocol for the industrial Internet."
The researchers presented their research at the International Solid-State Circuits Conference in San Francisco.
Source: MIT